Proxy vs Reverse Proxy Explained in System Design
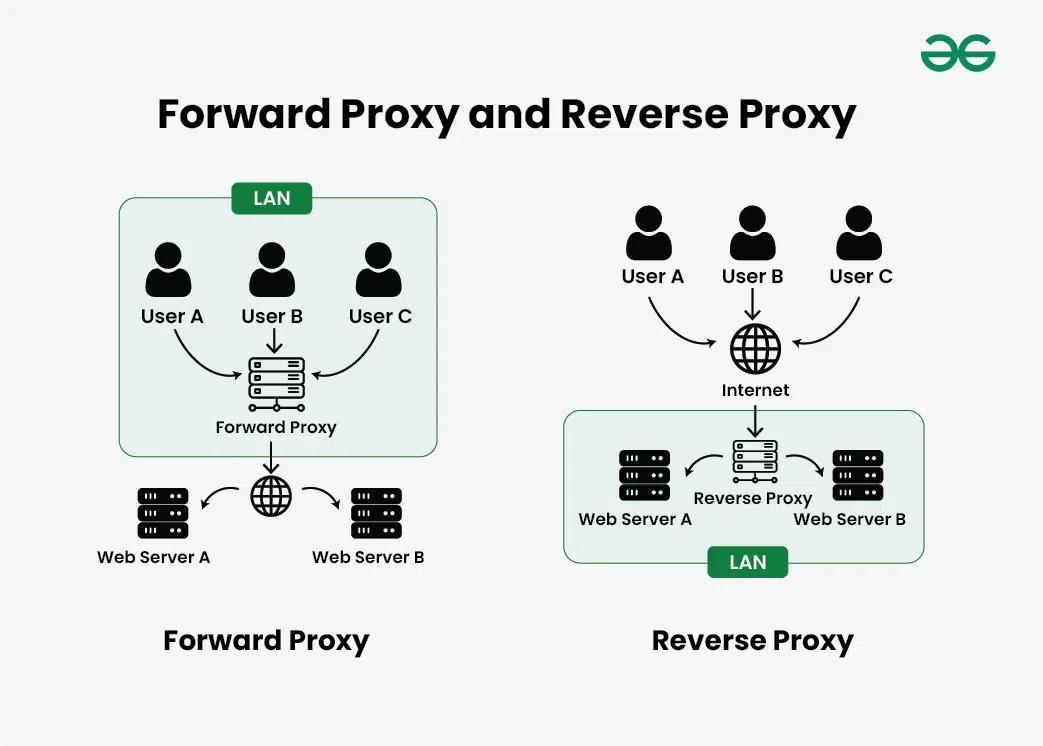
In modern web architecture, proxies are essential components used to improve security, performance, and scalability. Two commonly used types are Forward Proxy and Reverse Proxy. Although they may sound similar, they serve completely different purposes.
What is a Forward Proxy?
A forward proxy sits between the client and the internet. It acts on behalf of the client and forwards requests to external servers. This means the server does not know the actual client making the request.
For example, when using a VPN or corporate network proxy, your requests are routed through a forward proxy, hiding your identity.
How it Works
- Client sends request to proxy
- Proxy forwards request to server
- Server responds to proxy
- Proxy returns response to client
Use Cases
- Privacy and anonymity
- Content filtering in organizations
- Bypassing geo-restrictions
What is a Reverse Proxy?
A reverse proxy sits between the client and backend servers. It acts on behalf of the server and manages incoming requests. The client does not know which server is handling the request.
Reverse proxies are widely used in production systems to handle traffic, improve performance, and provide security.
How it Works
- Client sends request to proxy
- Proxy forwards request to backend server
- Server responds to proxy
- Proxy returns response to client
Use Cases
- Load balancing
- Caching responses
- SSL termination
- Hiding backend servers
Key Differences
| Feature | Forward Proxy | Reverse Proxy |
|---|---|---|
| Position | Client side | Server side |
| Purpose | Hide client identity | Protect backend servers |
| Usage | Privacy, filtering | Scaling, security |
Real-World Tools
Popular reverse proxy tools include NGINX and HAProxy, which are widely used to manage traffic and improve performance in large-scale applications.
Final Thoughts
A forward proxy focuses on protecting the client, while a reverse proxy focuses on protecting and optimizing the server. In modern system design, reverse proxies are more commonly used due to their role in scalability, load balancing, and security.